PCI DSS v4.0 brings stringent requirements to enhance data security in the face of evolving cyber threats. Notably, requirements 6.4.3 and 11.6.1 introduce critical mandates for monitoring and tamper detection to protect payment pages. These new stipulations are now incorporated into all Self-Assessment Questionnaire types, regardless of how many transactions they process, or whether they utilize a Third Party Service Provider (TPSP). However, merchants can claim to be SAQ A if they have “confirmed that their site is not susceptible to attacks from scripts that could affect the merchant’s e-commerce system(s).”
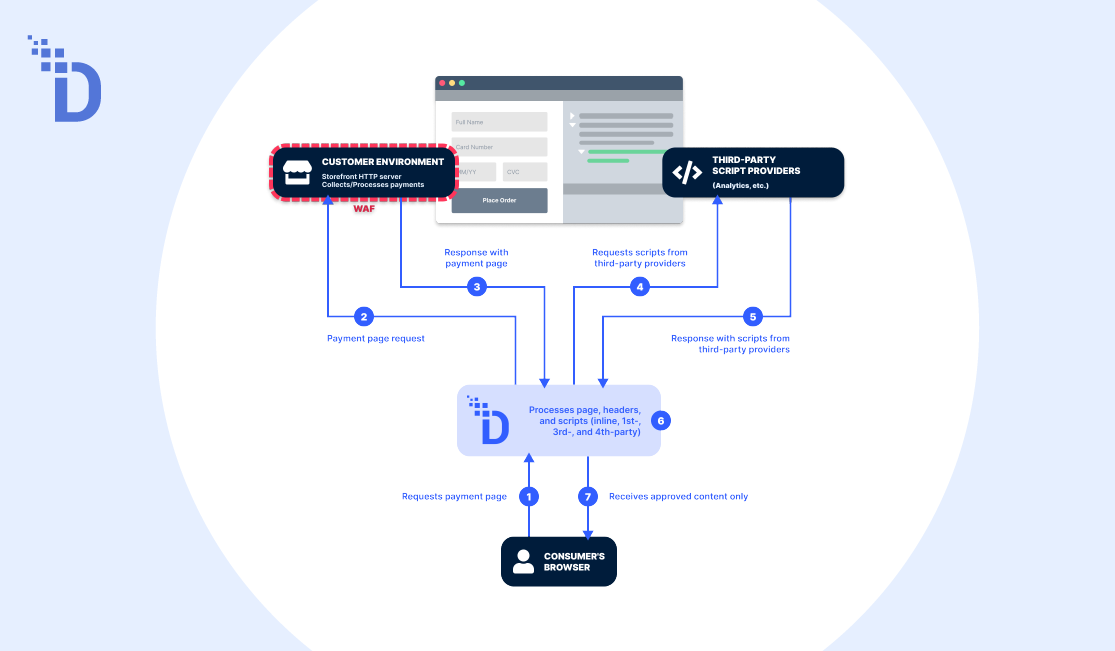
Requirement 6.4.3 focuses on the management and integrity verification of payment page scripts and also includes the pages and navigational flows leading up to the payment page. It mandates that “unauthorized code cannot be executed in the payment page as it is rendered in the consumer’s browser,” which requires creating and maintaining a comprehensive inventory of all scripts, and allowing only authorized scripts to be executed throughout the entire payment process.
Requirement 11.6.1 focuses on detecting unauthorized modifications to payment pages, including scripts and HTTP headers. It mandates these detection activities be performed at least once every seven days or at intervals determined by the entity’s targeted risk analysis, marking a significant shift towards proactive security measures.
Failure to comply with these new requirements can result in the suspension of payment processing, increased audit scrutiny, and reputational damage.