Uncover Structured and Unstructured Data Across Shadow IT, Forgotten Repositories, and Unsanctioned Applications
Schedule a DemoProliferation of sensitive data in on-premise, shadow IT, unknown repositories, and third-party SaaS and Cloud solutions make adhering to risk, compliance, governance and data residency regulations next to impossible.
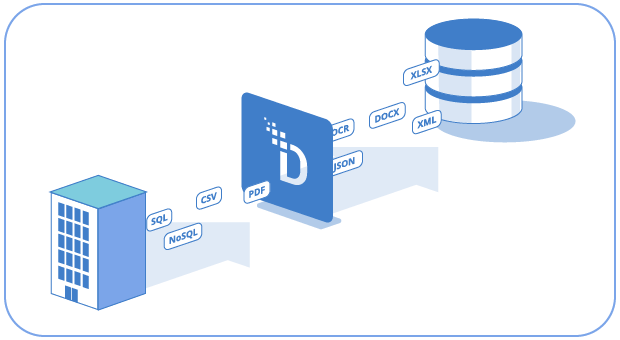
DataStealth Data Discovery gives you continuous, enterprise-wide visibility into where sensitive data lives and how it moves across your environment.

High-precision data handlers identify PII, PHI, and PCI data in databases, file shares (e.g., SMB/S3/SharePoint), logs, and other data stores, and can enrich findings with context such as system, owner, location, and residency.
Results then roll up in a single report that maps what was found, where it was found, and the level of sensitivity, not only providing you with a true and accurate risk profile, but also actionable intelligence and insights.
You can then turn insights into action using DataStealth’s Data Security Platform to apply tokenization, masking, or encryption to protect your sensitive data.
Turn discovery from a point-in-time exercise into a living inventory that powers PCI DSS, HIPAA, and GDPR compliance while keeping teams focused on action, not hunting.

Discover PII/PHI/PCI across databases and files alike including tables, data lakes, PDFs, scans, ZIPs, and nested/embedded content.
Take control by identifying hidden repositories and unsanctioned applications across your enterprise.
Get one unified inventory of every data source: known and unknown, on-premise, and in the cloud.
Locate and manage data across fragmented environments, no matter where it hides.
Satisfy PCI, GDPR, HIPAA, and governance mandates with verifiable discovery reports.

Identify every forgotten dataset and rogue repository, including those that your current tools may overlook.

Run scans on-demand, on your terms, with a platform built for enterprise scale.
Get started with a single DNS update. No agents. No code. No disruption.

Our customer, the Vice President of Data Security at a large global insurance provider, was tasked with ensuring that all data was accounted for and inventoried in its central ITIL-based repository. This repository was deployed to be the single source of truth for IT assets.

DataStealth ran a data discovery scan against a small segment of their network to confirm that the list of data sources they had in their tracking system was complete and accurate. It was not. DataStealth found 11 databases that were not listed, and where access was not tied to their federated credentials; in this case, Azure AD.
DataStealth was deployed by each business unit to scan all network segments to provide a complete and accurate inventory of data sources per business unit, which was then uploaded to their central ITIL-based repository. Scans were run ongoing on a scheduled basis to ensure that any new data sources were quickly identified and remediated.

Get a quick look at how DataStealth can work in your environment
SCHEDULE A CALL