DataStealth deploys directly inside your data center – on bare metal, VMs, containers, or Kubernetes – so sensitive information never leaves your trust boundary.
From regulated workloads to tightly controlled or even air-gapped environments, you maintain full control without sacrificing protection.

Tokenize or mask fields in real-time by placing DataStealth between apps, users, or services – no code changes required.
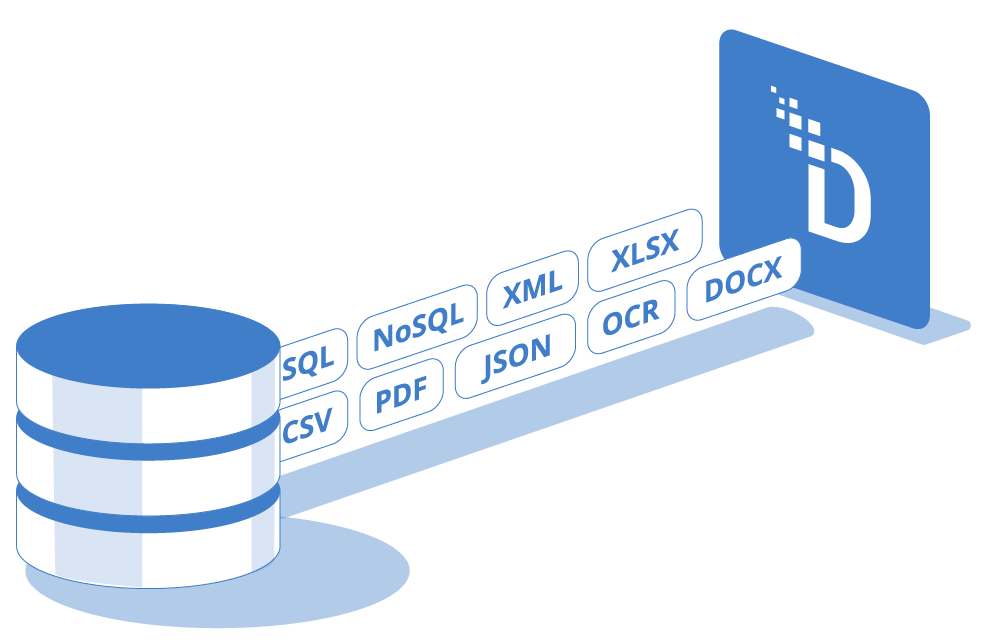
Enforce field-level protection on SQL or NoSQL traffic without modifying your database engine.

Run DataStealth alongside microservices to enforce per-service policies with minimal development effort.
Discover, classify, and protect sensitive data at scale across files, data lakes, and event streams.
Active-active nodes behind your load balancers keep protection continuous – even in restricted or air-gapped deployments.
Horizontally scale brokers and workers across bare metal, VMs, or Kubernetes to meet any throughput or latency target.
Policies are managed as code with versioning, approvals, and rollbacks – so enforcement is consistent and error-free.

Every action is logged and exportable to your SIEM, giving you complete traceability and real-time compliance reporting.
Automatically scrub sensitive data before it hits logs, tickets, or traces.

See how DataStealth deploys in your data center, secures legacy and modern systems alike, and enforces protection at scale – all without adding complexity or slowing down your teams.
On-premise deployment keeps all sensitive data processing – i.e., discovery, classification, tokenization, masking, and encryption – inside your trust boundary.
For organizations in financial services, insurance, healthcare, and government, this is often a regulatory requirement rather than a preference: certain data categories must never leave a controlled perimeter, and compliance frameworks like PCI DSS and HIPAA impose strict requirements on where cardholder data and protected health information can be processed and stored.
On-premises deployment also eliminates third-party cloud provider risk, i.e., the organization retains full control over key management, access policies, and audit trails.
For organizations that need the flexibility of both models, DataStealth supports hybrid and cloud deployment alongside on-premise, all managed under a single policy framework. For a broader perspective on platform selection, see The Ultimate Guide to Data Security Platforms.
Yes. DataStealth is purpose-built for environments where internet connectivity is unavailable or prohibited, including classified government networks, critical infrastructure operators, and defence-sector facilities.
The platform runs entirely within your data centre on bare metal, VMs, containers, or Kubernetes clusters with no dependency on external cloud services.
Policy management operates as code with local versioning, approvals, and rollbacks, and all key management integrates with your own on-premise KMS or HSM through full BYOK (Bring Your Own Key) and dual-control mechanisms.
Active-active node configurations behind your internal load balancers maintain continuous protection even in fully disconnected deployments.
For organizations managing mainframe workloads in restricted environments, DataStealth protects legacy systems without requiring code rewrites or agent installations.
On-premise deployment directly supports compliance by ensuring that sensitive data never crosses the perimeter boundary for processing.
Under PCI DSS, on-premise tokenization means that downstream systems that store or process tokens are removed from the audit scope entirely, reducing the number of systems subject to assessment and lowering compliance costs.
Under HIPAA, on-premise encryption and masking of ePHI satisfy the Security Rule's requirements for access controls and encryption while keeping all processing within a covered entity's own infrastructure.
DataStealth's audit logging exports to your SIEM, providing the traceability that QSAs and auditors require.
For organizations subject to data residency regulations, on-premise deployment guarantees that no data processing occurs outside the mandated jurisdiction.
DataStealth supports four on-premise deployment models to match different enterprise architectures.
All models support protocol handlers for HTTP(S), gRPC, and GraphQL, and data type handlers for structured, semi-structured, and unstructured formats.
See the full platform overview for how these models integrate across your stack.