DataStealth delivers enterprise data encryption solutions across on-prem, cloud, SaaS, mainframe, and AI environments with just a DNS change.
SEE A LIVE DEMO
Sensitive data sits in cleartext across databases you – and don’t know – about, file shares your teams have forgotten, SaaS platforms you didn’t approve, and AI pipelines you haven’t certified.
Use DataStealth to find every sensitive field – whether on-prem, in the cloud, in SaaS, or in AI – and protect it on the spot with field-level, format-preserving encryption.

4.8/5 rating on G2 and other review platforms for data-centric security and ease of deployment.

Air Canada Vacations chose DataStealth to provide additional solutions to secure their new partner integration. It worked so well that they now look to DataStealth to secure all of their future integrations.

DataStealth is recognized in Forrester’s Data Security Platform Landscape Report and trusted by highly regulated organizations that cannot afford data exposure or downtime.
Mainframes, Snowflake, on-prem SQL servers, SaaS, file stores, APIs, and AI pipelines each pose distinct data exposure risks.
Traditional encryption solutions force security teams into one of three tradeoffs: integrate system-by-system, add SDK work to every application, or to deploy and maintain endpoint agents. DataStealth eliminates that sprawl.
It operates in-line at the network layer, discovering and protecting sensitive data before it’s stored, queried, copied, or exposed.
One deployment model applies field-level encryption (as well as data tokenization and dynamic data masking) across systems you already run, without changing application code, installing agents, or rewriting schemas.
Detect PAN, SSN, PHI, PII, credentials, and regulated identifiers across databases, file stores, APIs, SaaS, streams, and AI pipelines.

Apply field-level encryption, tokenization, or masking in-line before sensitive data is written or exposed. Policies determine the right treatment per field.
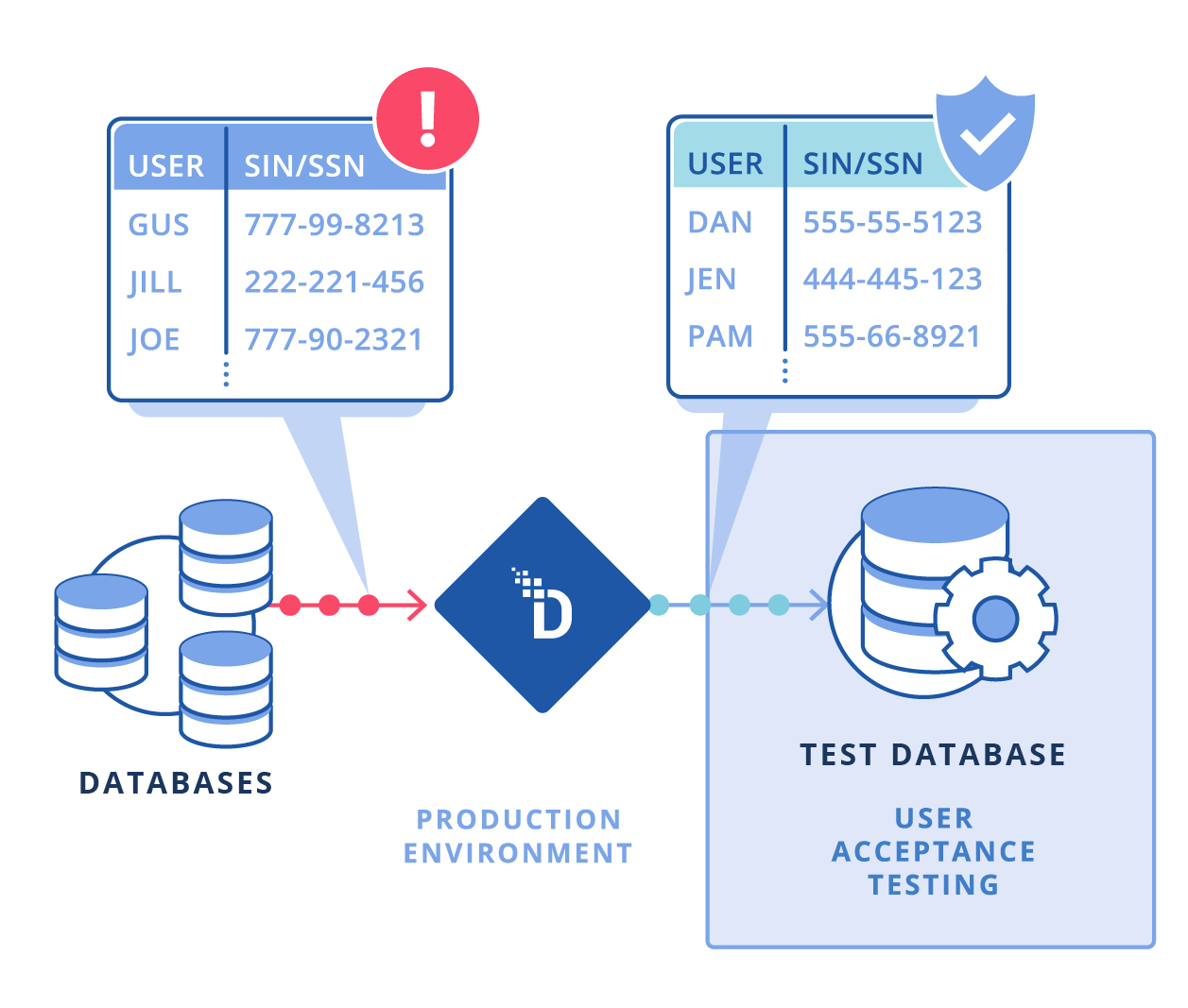
Preserve length, format, character set, and referential utility so downstream systems, validation rules, analytics, and classification workflows keep working.
Show cleartext, masked values, tokens, or encrypted data based on user role, geography, device, purpose, and policy. Same database, different authorized views.

Use horizontally scalable, stateless brokers designed for enterprise throughput across application, database, API, and file traffic.

Log discovery, protection, reveal, detokenization, and policy events for SIEM export, audit evidence, and PCI DSS, HIPAA, and GDPR readiness.
DataStealth gives enterprises a complete data-centric security posture from a single policy layer. Use encryption where data must be recoverable, tokenization where systems do not require real sensitive data, and masking where users need limited visibility.
Protect individual sensitive fields instead of entire systems. In one record, a PAN can be tokenized, a name masked, and a diagnosis encrypted based on policy.

Preserve length, character set, and structure so that legacy applications, validators, payment flows, and downstream systems continue to work.
Use deterministic tokens for joins, deduplication, and analytics. Use randomized tokens when privacy is more important than referential consistency.
Support BYOK, HYOK, cloud KMS, and on-prem HSM models with per-tenant key isolation, rotation, and enterprise key custody.

Reveal only what each user or workflow needs: last four digits, initials, redacted values, masked fields, or full cleartext.

Log discovery, protection, reveal, detokenization, and policy events for SIEM export, audit evidence, and PCI DSS, HIPAA, and GDPR readiness.

Manage protection rules with versioning, approvals, rollback, and auditability so security policies can move at rapid delivery speed.

Discover and protect sensitive data across databases, APIs, Kafka streams, SaaS platforms, Word files, PDFs, spreadsheets, images, and more.

Deploy with a DNS change. No application rewrites, endpoint agents, collectors, or schema changes required.
Enterprise data estates rarely fit one architecture. Critical data resides in private data centers, cloud platforms, SaaS tools, file shares, and legacy mainframes simultaneously.
DataStealth gives security teams a consistent way to discover, classify, and protect sensitive data across those environments without forcing infrastructure consolidation or application rewrites.
LEARN MORE ABOUTProtect sensitive data across bare metal, VMs, containers, Kubernetes, private data centers, and air-gapped environments.
Apply field-level encryption, tokenization, and masking across AWS, Azure, and GCP while keeping processing local to the approved region.
Enforce consistent policies across legacy systems, private infrastructure, and cloud workloads with centralized visibility and local control.
Protect IBM z/OS, AS/400, DB2, and legacy application traffic without modifying core applications.
An enterprise data encryption solution protects sensitive data — PII, PHI, PANs, and other regulated fields — by transforming it into unreadable formats or replacing it with non-sensitive surrogates.
These solutions go beyond file-level encryption tools by covering databases, APIs, file stores, SaaS applications, and streaming platforms at the scale enterprises require. The goal is to ensure that even if systems are compromised, the data inside has no exploitable value.
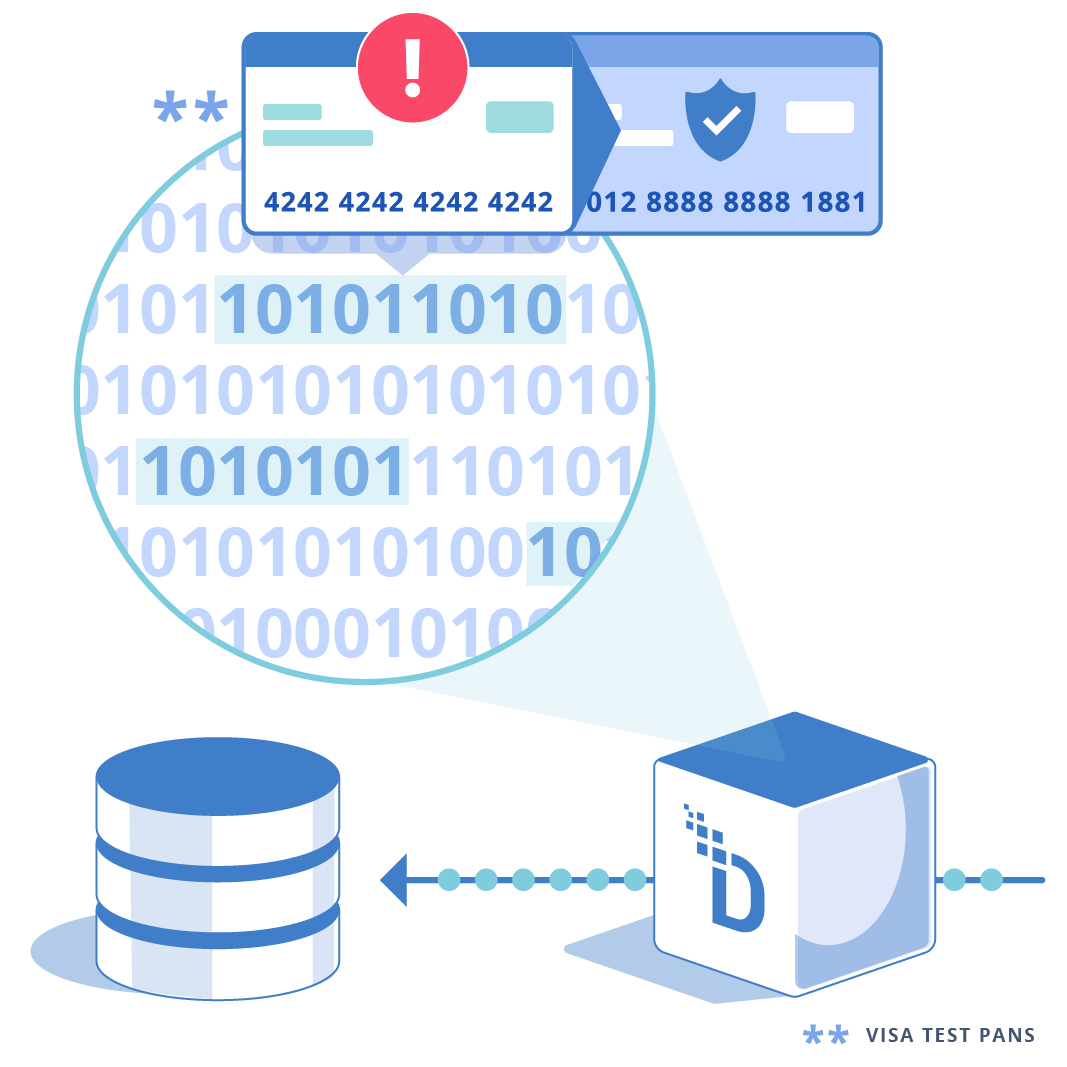
Encryption transforms data using a cryptographic key — the original is recoverable by authorized parties holding the key. Tokenization replaces data with a surrogate that has no mathematical relationship to the original.
Both protect sensitive data; they serve different purposes. Use encryption when the original value must be recoverable (e.g., processing a payment). Use tokenization when downstream systems do not need the original value (e.g., analytics, reporting). DataStealth lets you apply both per-field and per-policy.
At minimum: AES-256 for symmetric encryption, FIPS 140-2 validated implementations, TLS 1.2+ for data in transit, and FPE (FF1/FF3) for format-sensitive fields. DataStealth supports all of these encryption standards from a single platform.
Under PCI DSS 4.0, encrypting cardholder data satisfies Requirement 3 for protecting stored account data. DataStealth implements field-level encryption with strong key management (AES-256, BYOK, HSM integration).
To go further, DataStealth augments encryption with tokenization — replacing PANs with tokens so systems that do not need the original value can be removed from CDE scope. Customers have reduced audit scope by up to 90% by combining encryption and tokenization.
Well-architected solutions introduce negligible latency.
Storage-layer TDE adds minimal CPU overhead. Inline solutions like DataStealth use stateless, horizontally scalable brokers with in-memory processing — performing data protection at wire speed.
Network-based approaches outperform API-based calls, which add network round-trip delays. High-frequency payment and application environments maintain required throughput levels.
Yes. DataStealth deploys with a DNS change — no APIs, agents, collectors, or schema rewrites. It operates at the network layer between applications and data stores, applying protection transparently.
This enables rapid deployment in complex, legacy, and hybrid environments. SDK and API integration is available for teams that prefer direct control — but it is optional, not required.
Most DSPMs (Varonis, BigID, OneTrust) provide visibility — discovery and classification — but not protection. If your DSPM cannot tokenize, encrypt, or mask data, you need a separate tool or a unified data security platform that does all three.
DataStealth combines discovery, classification, and protection in a single platform — so you do not need to stack vendors to close the gap.